External Attack Surface Management
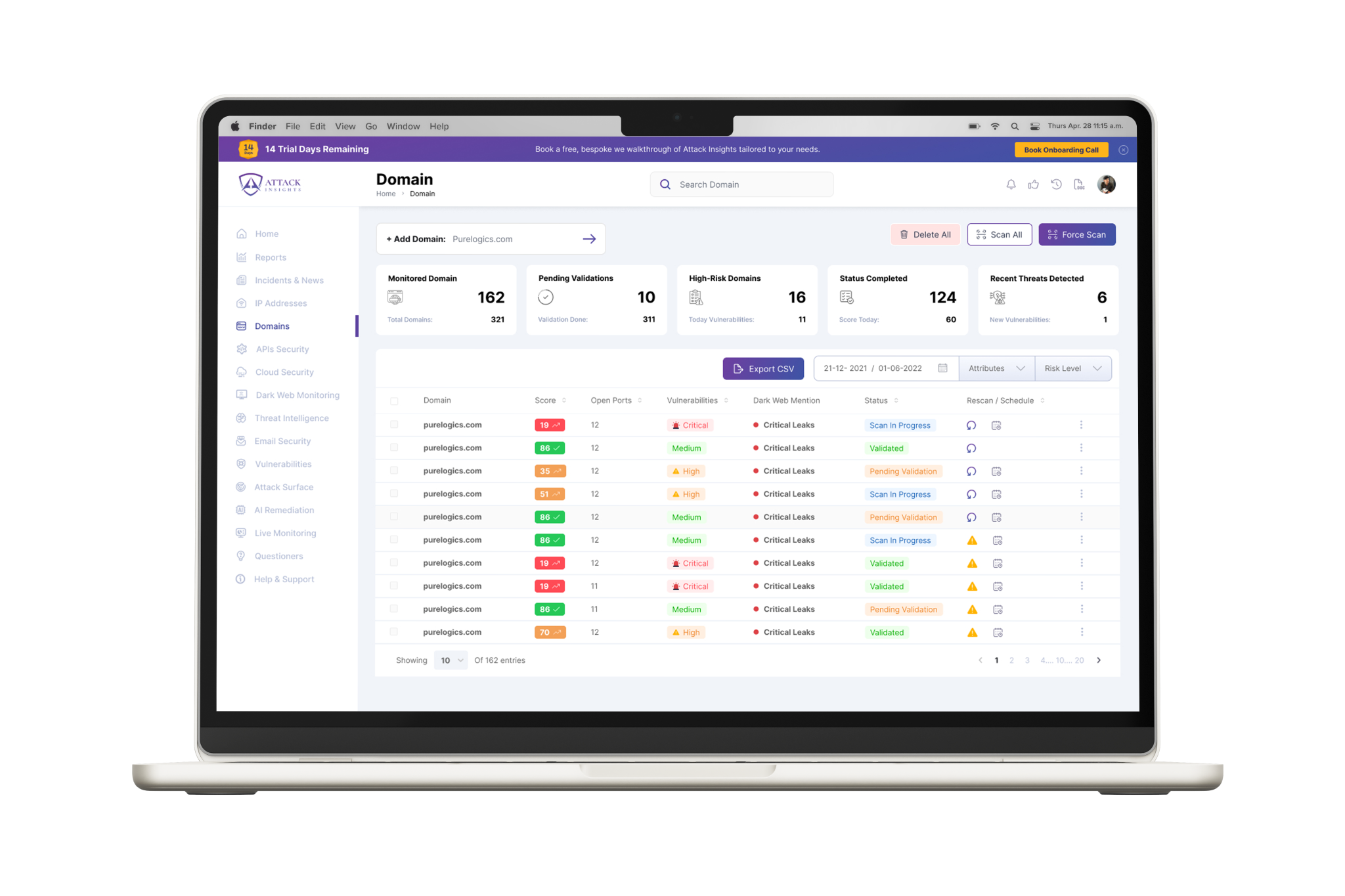
Continuous discovery and security monitoring of all domains, subdomains, IPs, and cloud services.
Attack Insights provides a proactive Attack Surface Management (ASM) platform to discover, analyze, and neutralize threats before they impact your business.
Shadow IT, forgotten subdomains, and exposed developer secrets create a landscape of unknown risks. If you can't see it, you can't protect it. This visibility gap is where attackers thrive.
Attack Insights illuminates your entire external footprint. We provide the continuous visibility and actionable intelligence needed to shrink your attack surface and neutralize threats proactively.
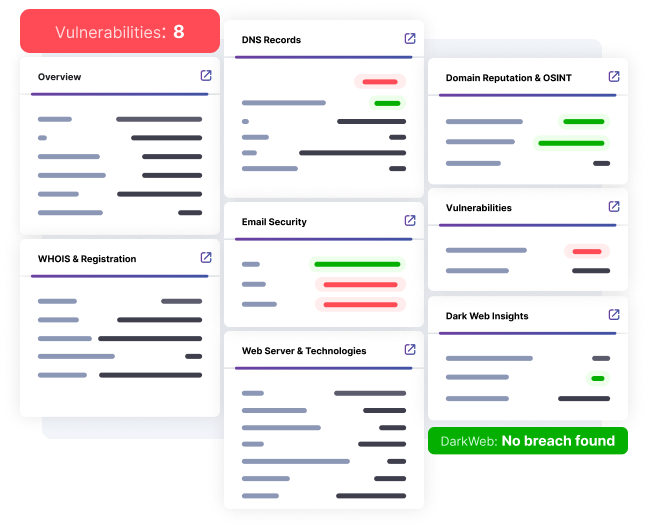
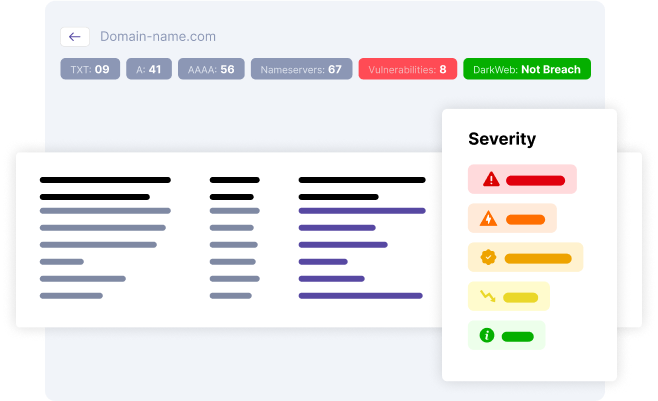
Our integrated modules work together to provide a 360-degree view of your external security posture.
Continuous discovery and security monitoring of all domains, subdomains, IPs, and cloud services.
Aggregated data from open and closed sources, providing real-time analysis of TTPs and IOCs.
24/7 surveillance of darknet forums and markets for leaked credentials, PII, and brand abuse.
Detect phishing campaigns in real-time and monitor for leaked or misconfigured API keys.
Attack Insights delivers critical intelligence tailored to the needs of key roles in your organization.
Accelerate alert triage with high-fidelity, contextual alerts that reduce noise and investigation time.
Gain strategic risk visibility with comprehensive reporting for board-level conversations and compliance.
Manage multiple clients efficiently with a scalable, multi-tenant architecture designed for service providers.
Automate evidence collection and simplify audits for regulations like DORA, GDPR, and KVKK.
Seamlessly push actionable intelligence into your existing SIEM, SOAR, and ticketing systems to enhance your established workflows.
Your common questions, answered.