March 2026’s Most Critical Vulnerabilities: Why Management Planes, Identity Layers, and Core Enterprise Platforms Remain High-Value Targets
As of March 25, 2026, this month’s vulnerability landscape highlights a familiar but increasingly dangerous pattern: attackers continue to prioritize systems that sit closest to enterprise control, authentication, and business continuity. The most severe issues disclosed in March are not random edge-case bugs. They affect security management consoles, identity infrastructure, and SAP environments that often sit at the center of operational decision-making. In practical terms, that means the impact of exploitation is no longer limited to one server or one application. In the wrong conditions, a single exposed weakness can translate into administrative control, lateral movement opportunities, or direct business disruption.
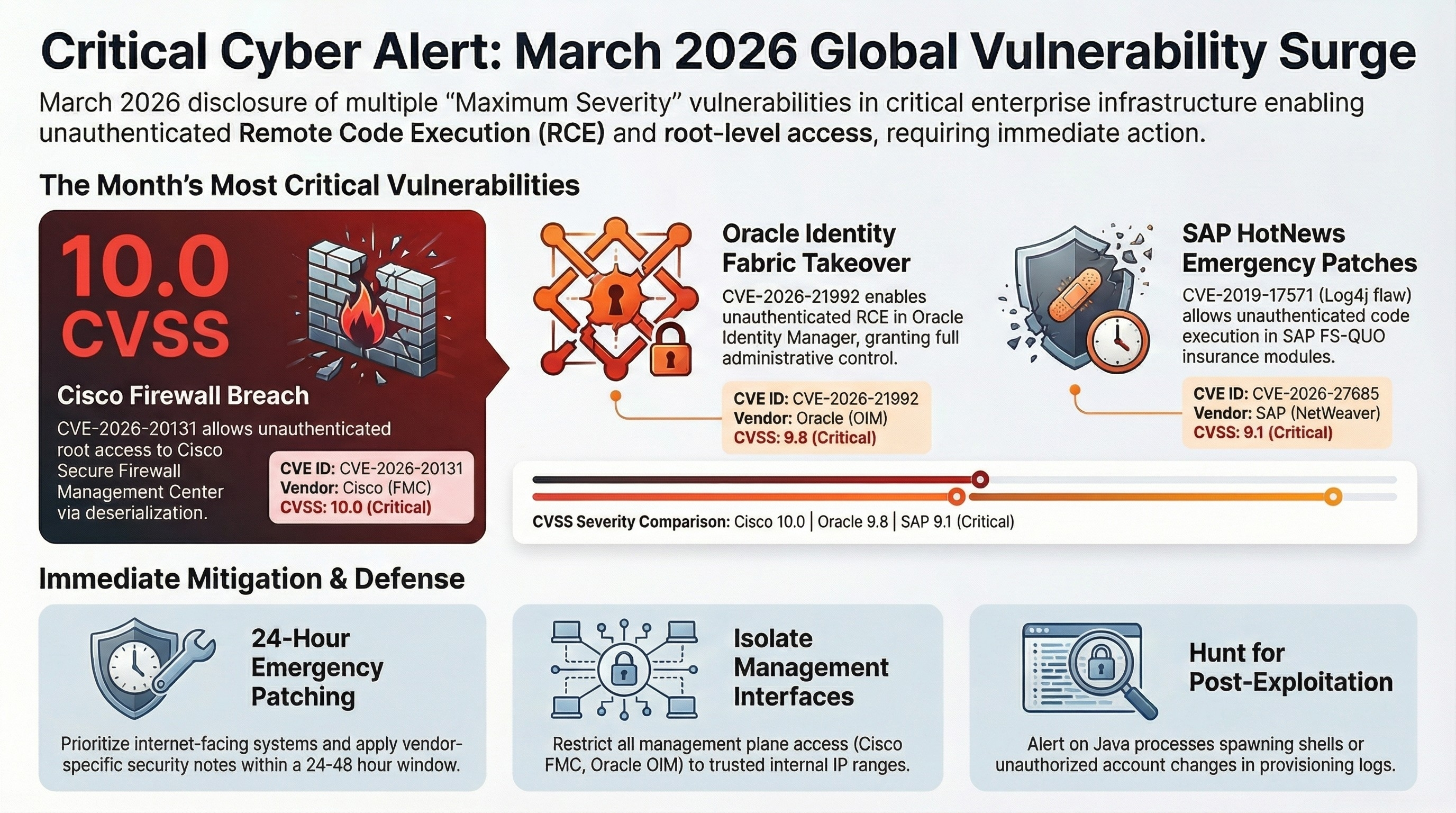
One of the clearest examples is CVE-2026-20079, a critical vulnerability in Cisco Secure Firewall Management Center (FMC) with a CVSS score of 10.0. According to NVD, the flaw allows an unauthenticated remote attacker to bypass authentication and execute script files on an affected device, ultimately obtaining root access to the underlying operating system. What makes this especially serious is not only the score, but the target: FMC is part of the management plane for firewall infrastructure. When a vulnerability affects the very layer responsible for visibility and policy orchestration, the security risk extends beyond host compromise and into governance, segmentation, and centralized control.
A second Cisco issue, CVE-2026-20131, is equally severe and arguably more operationally urgent. This vulnerability, also rated CVSS 10.0, affects the FMC web-based management interface and enables unauthenticated remote code execution as root through insecure deserialization of a user-supplied Java byte stream. NVD notes that the attack surface is reduced if the FMC management interface is not publicly reachable, which reinforces a long-standing security principle that management interfaces should never be unnecessarily exposed to the internet. More importantly, this is not a purely theoretical concern: the vulnerability has been tied to active exploitation reporting, and CISA has listed it in the Known Exploited Vulnerabilities Catalog. AWS also reported an Interlock ransomware campaign exploiting this issue against enterprise firewalls.
The Oracle ecosystem also saw a highly critical development with CVE-2026-21992, affecting Oracle Identity Manager and Oracle Web Services Manager. Oracle’s March 2026 security alert states that the vulnerability is remotely exploitable without authentication and may result in remote code execution. The affected product versions include 12.2.1.4.0 and 14.1.2.1.0 for both product lines. From a security architecture standpoint, vulnerabilities at the identity and services-management layer deserve immediate executive attention because they sit close to authentication, entitlement, and service trust boundaries. When these layers are exposed, the downstream effect can exceed a single application compromise and reach directly into enterprise access models.
SAP’s March 2026 Security Patch Day further confirmed that business-critical application stacks remain a prime target class. SAP reported 15 new security notes on March 10, 2026, including two critical issues that stand out from a risk-prioritization perspective. The first is CVE-2019-17571, listed by SAP in March 2026 as a Code Injection vulnerability in SAP Quotation Management Insurance (FS-QUO 800) with a CVSS score of 9.8. The second is CVE-2026-27685, an Insecure Deserialization vulnerability in SAP NetWeaver Enterprise Portal Administration (EP-RUNTIME 7.50) with a CVSS score of 9.1. Both were classified by SAP as critical items in the month’s patch cycle.
The SAP NetWeaver issue is particularly important because it illustrates a nuance that often gets lost in high-level vulnerability reporting. Not every critical vulnerability is built around a simple anonymous internet-to-RCE scenario. In the case of CVE-2026-27685, NVD states that exploitation involves a privileged user uploading untrusted or malicious content, which can then have high impact on confidentiality, integrity, and availability. Onapsis similarly notes that only the requirement for high privileges prevented the issue from being scored even higher. This matters because real-world enterprise breaches frequently involve compromised admin accounts, abused internal privileges, or chained exploitation paths. A vulnerability that requires elevated permissions is not low risk when privileged accounts themselves remain a high-value attack target.
Taken together, the March 2026 picture is not just a list of severe CVEs. It is a map of where attackers continue to find leverage. Management consoles, IAM-adjacent services, and core enterprise platforms remain disproportionately important because they concentrate control, visibility, and trust. A flaw in one of these layers often gives an attacker more than code execution; it offers position, persistence, and operational reach. That is why the most important question is no longer whether a vulnerability is technically critical. The better question is whether it sits on a path to centralized administration, identity enforcement, or core business process execution.
For security teams, the response should be disciplined and immediate. Internet-facing management interfaces should be reviewed first. Patch prioritization should give extra weight to pre-auth flaws affecting firewall management, IAM services, and SAP administration layers. Exposure management should be treated as a control in its own right, not merely as an inventory exercise. And where immediate patching is not feasible, compensating controls around segmentation, access restriction, and privileged account hardening need to move from best practice to mandatory action. Cisco, Oracle, and SAP have all published remediation or patch guidance for the issues above, and in the case of Cisco FMC, active exploitation indicators make delay especially costly.
March 2026 has reinforced a simple operational truth: the highest-risk vulnerabilities are often the ones that target systems designed to manage, authorize, or orchestrate everything else. That is exactly why patch management cannot be handled as a routine IT workflow alone. In these cases, it is a core security decision with direct implications for resilience, containment, and business continuity.